Unlock the Power of Security Automation: Threat Intelligence Management
Chris JacobThreat intelligence has become a significant input to the overall ecosystem that organizations leverage in their security footprint. Managing that data and the contextualization required to develop useful information can be daunting for fledgling and established organizations. I will discuss ways to automate some of the repetitive tasks and fuel other areas of the security organization to help them better achieve their mission sets.
A few years back, the advent of the SOAR platform held a lot of obvious opportunities for finding efficiencies in threat intelligence management. While some of these opportunities have been realized, some unexpected roadblocks have also become apparent. The flexibility of these systems introduced complexities. Often the platform would be owned by another team, making changes and updates to workflows difficult.
The industry has recently started talking about Extended Detection and Response, or XDR. To me, this is an up-and-coming concept and, as it continues to emerge and solidify,it fits perfectly into what we have been working with our customers to accomplish. XDR has to be a defined practice, not just a tool you purchase to check the box. When we step back and look at the importance of threat intelligence in threat hunting, vulnerability management, combating spear phishing, and on and on, the concept of a single source of truth at the center of all of those efforts becomes paramount. The practice of threat intelligence management is at the core of all this.
As we dive into the use case of threat intelligence management, it’s important to point out that the National Institute of Standards and Technology (NIST) defines threat intelligence as “Threat information that has been aggregated, transformed, analyzed, interpreted, or enriched to provide the necessary context for decision-making processes.” This is a definition I agree with. There are a lot of great intel vendors out there, but even the best threat data needs to be contextualized by the consuming organization to get the most value and reduce the noise as much as possible.
The aggregation of threat data seems like apparent low-hanging fruit that any intelligence platform would be able to handle with ease. However, this is not always the case. Working with multiple copies of a single piece of information can lead to confusion, wasted time re-enriching data, and the risk of missing something important. The process of normalization and deduplication is critical to ensure everyone is working from the same starting point.
Once we have a clean data set, the work of the Intelligence Analyst can begin. Teams must have well-established processes to enrich that data to begin the transformation into intelligence. Much of this enrichment process can be tedious and eat up analyst cycles. This is the first opportunity to introduce automation. If we can define a process that says whenever data meets this criterion, do this with it, we should be able to automate that task.
For example, let’s say that in my shop, we take all new indicators from our OSINT providers that have been modified in the last 24 hours and enrich them with Shodan. To achieve this, I simply create a “Smart Collection” or filter in my Threat Library for the sources I want and any items that have been modified in the last 24 hours.
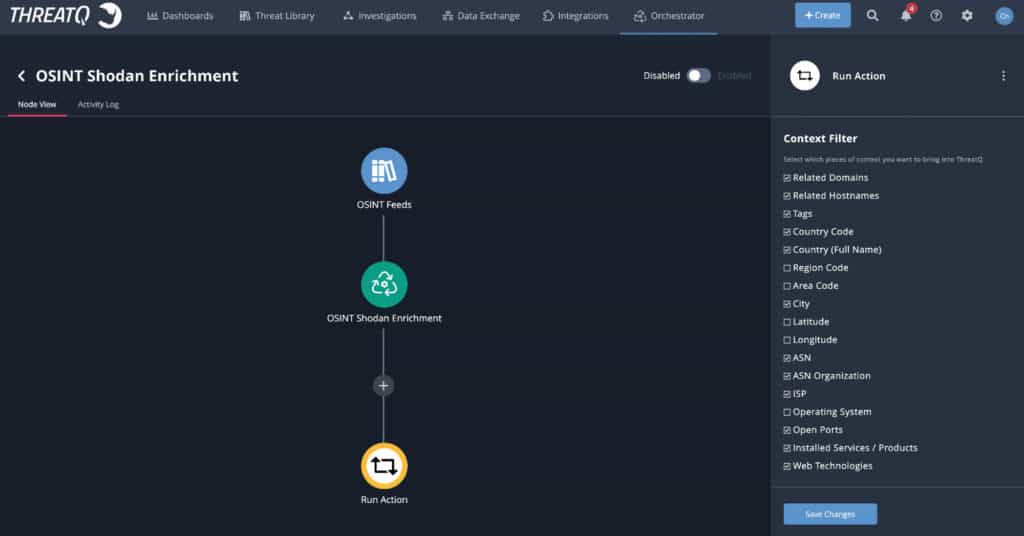
One of the things that are returned from this enrichment is a country code that I could use as part of my user-defined scoring policy to “bubble up” the information that is important to my organization.
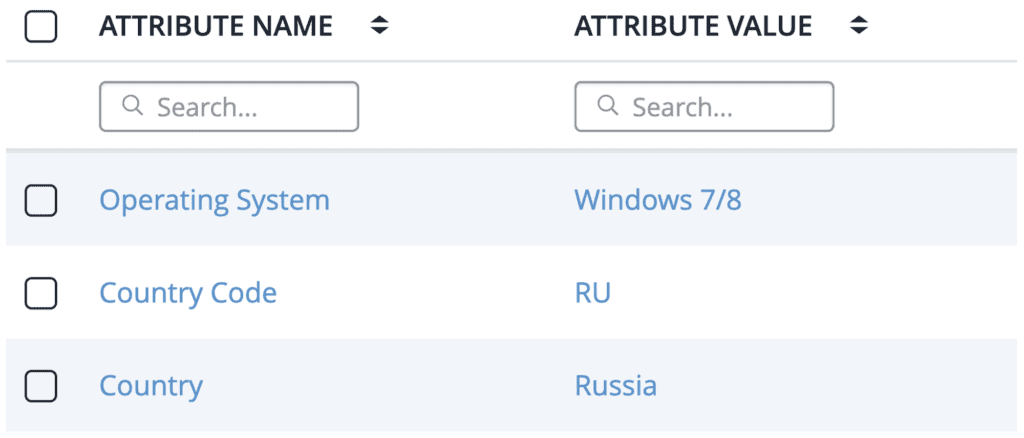
From this simple automation, I can start to build out lists of things we as an organization need to keep an eye on. I can start sharing this information with other areas of the security organization, which could include;
SOC (SIEM Tool)
Based on the country code and a relationship to a particular piece of malware or threat actor, send all related indicators to the SIEM for alerts when information is matched. In addition to the SOC receiving and working on any alerts from the SIEM, my intelligence platform should also be notified. This allows me to continue to prioritize this information using my scoring algorithm and refine my intelligence.
Threat Hunting
Based on the country code, and a relationship to a particular piece of malware or threat actor, I can use MITRE Attack correlation to provide my Threat Hunting team with a set of TTPs to be on the lookout for as they hunt the network looking for malicious activity. Bidirectional integration with their threat hunt team ensures they will always have the latest, most refined intelligence. As they mark items confirmed or false, that information is instantly available in the Threat Library.
Vulnerability Management
Based on the country code and a particular piece of malware or threat actor, I can pivot on what vulnerabilities are known to be in use. Providing these CVEs to the Vulnerability Management team will help them prioritize which assets should be patched. In the event that patching is not immediately possible, my Threat Library allows me to look for compensating controls such as firewall or IPS rules that can be put in place.
These are, of course, simplified examples that I’ve used to point out a use case of threat intelligence management and its importance in the overall security practice. I would emphasize that defining the process is key, and most organizations have already started down this path. The next step is to look for opportunities to free up valuable analyst resources by looking for ways to automate these processes.
This use case is at the very beginning of a critical cycle of refinement of threat intelligence to bring demonstrable value to the work that the CTI team performs. In upcoming blog posts, my colleagues and I will dive deeper into spear phishing triage and vulnerability management. and tackle the big picture around extended detection & response and what makes a best of breed XDR tool.

0 Comments