What is a SOAR Platform?
Regardless of the approach, threat intelligence is critical to ensure a SOAR platform is executing the right actions and using the right data. Data, especially with the increasingly large data sets security teams use, can be extremely noisy. Automate noise and the result will be amplified noise. A data-driven approach to SOAR provides high confidence in the intelligence being used, the decisions that are made and the incident response workflows that are executed. The ThreatQ platform is the engine behind a data-driven, no-code/low-code approach aggregating, scoring, and prioritizing intelligence so that security operations can operate more efficiently and effectively.
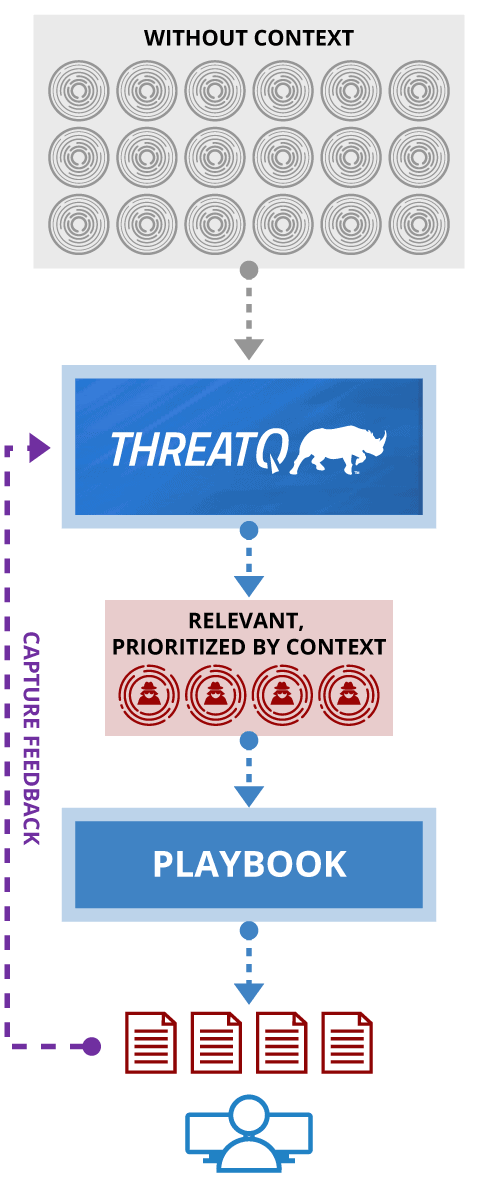
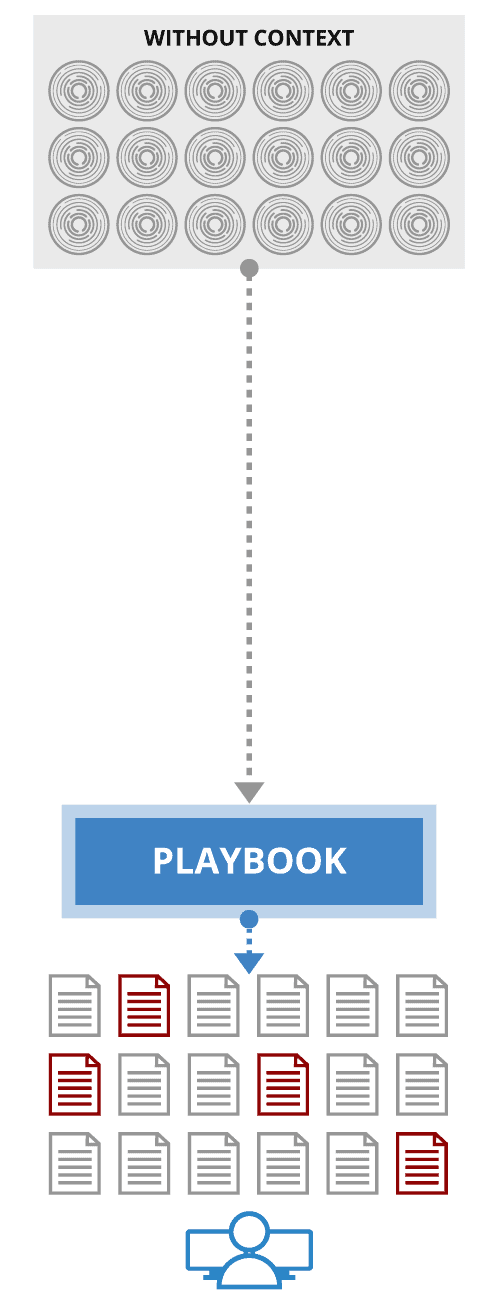
COMPARISON BETWEEN PROCESS-DRIVEN AND DATA-DRIVEN
DATA-DRIVEN
- All data is contextualized, Playbook run, if needed, is based on context
- Output is relevant and high priority, and far fewer for analysts to review
- Data captured for further analysis and improvement
PROCESS-DRIVEN
- Takes ALL data inputs and runs ALL through playbooks
- Report/dossier for EVERY input, requiring analyst to review each one
- Output NOT captured or used programmatically
It Starts With the Right Data
Confidence starts with
the Right Data
The right idea leads to
Confident Decision
Making
Confident decision
making can lead
to Automation
HOW THREATQ WORKS:
DATALINQ ENGINE™
Combine Threat Data From Any Source, Internal And External
Connecting disparate systems and sources, this adaptive data engine imports and aggregates external and internal data; curates and analyzes data for decision making and action; and exports the right intelligence to the right tools at the right time to accelerate threat detection, investigation and response (TDIR).
- INGEST and aggregate structured and unstructured data via Marketplace apps and an open API
- NORMALIZE automatically from different sources, formats and languages into a single object
- CORRELATE across atomic pieces of data to identify relationships and provide a unified view
- PRIORITIZE via customer controlled, dynamic scoring to ensure relevance and filter noise
- TRANSLATE data into the format and language necessary for consumption across systems
THREAT LIBRARY
Shared Contextual Intelligence
Using ThreatQ as a threat intelligence platform equips you with a threat library that automatically scores and prioritizes intelligence based on parameters you set. Prioritization is calculated across many sources, both external and internal, to deliver a single source of truth using aggregated context. This removes noise, reduces false positives and enables users to focus on the data that really matters.
- Extensible Data Model
- Consolidated view, unified opinion
- Automatically prioritize based on all sources
- Custom enrichment source for existing systems
- Define Smart Collections for workflows and automation
THREATQ TDR ORCHESTRATOR
Data-drive, no-code/low-code automation
ThreatQ TDR Orchestrator simplifies orchestration and automation through a no-code/low-code, data-driven approach which “puts the smarts into the platform.” ThreatQ does this through data curation and extracts much of the complexity of process-driven playbooks. Update the platform once vs having to update dozens of playbooks.
- Easy to set-up and maintain
- Reduce playbook runs by 80%
- Ensure output is relevant and high priority
- Learn from the actions taken, and improve over time
- Harness Generative AI and Natural Language Processing (NLP)
THREATQ INVESTIGATIONS
The industry’s first cybersecurity situation room
ThreatQ Investigations removes the collaboration and coordination inefficiencies that exist across security operations to accelerate detection and response. As the first cybersecurity situation room, it streamlines investigations and improves active collaboration among and across teams. Team leaders can direct actions, assign tasks and see the results unfold in near real time.
- Fuse together threat data, actions, and users
- Combine automation and human intelligence
- Accelerate investigation, understanding and response to threats
- Build incident, adversary and campaign timelines
- Drive down mean time to detect (MTTD) and mean time to respond (MTTR)
MARKETPLACE
Open and Extensible Architecture Enables Robust Ecosystem
Get more from your existing security investments by integrating your tools, teams and workflows through standard interfaces and an SDK/API for customization.
- Bring your own connectors and tools
- SDK / API for customization
- Standard STIX/TAXII support
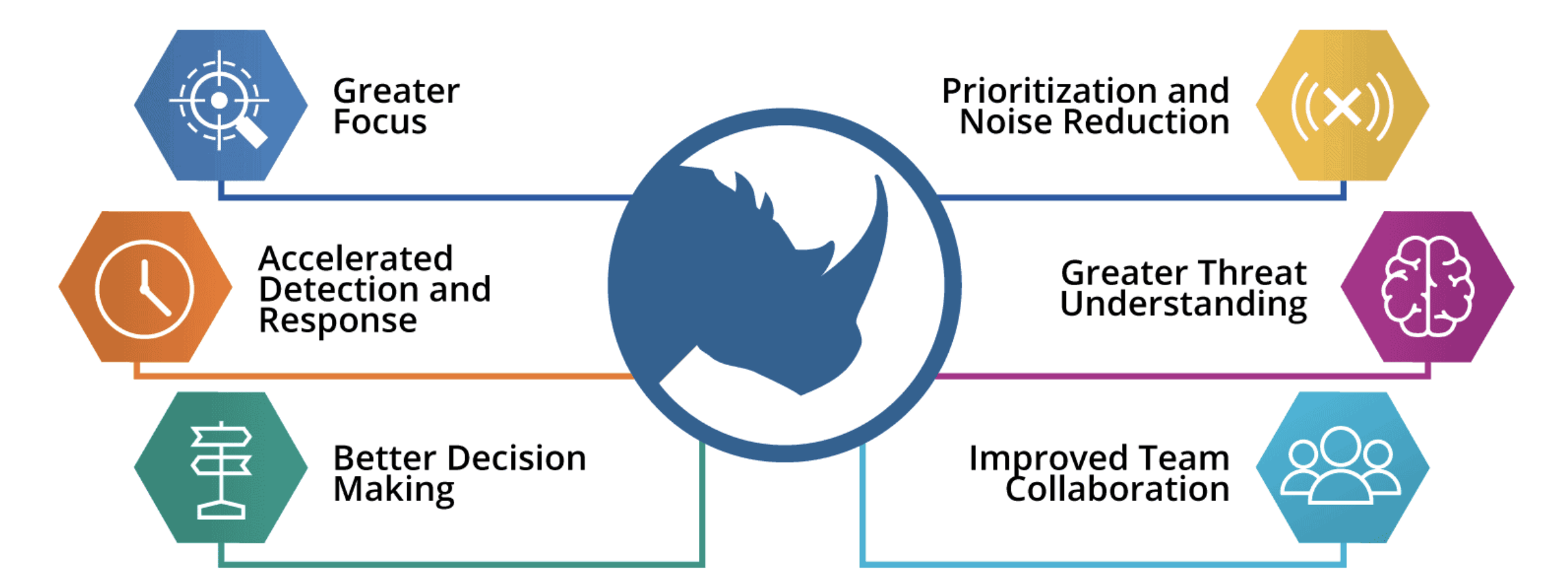
WHAT A SOAR PLATFORM SHOULD BE
With ThreatQ serving as a SOAR platform, a company can unify its cybersecurity infrastructure and components into a single defense ecosystem, allowing them to accelerate security investigations, improve the mean time to respond to cyberthreats and increase ROI.