How ThreatQ fills a SOAR platform need

SOAR Platform Capabilities
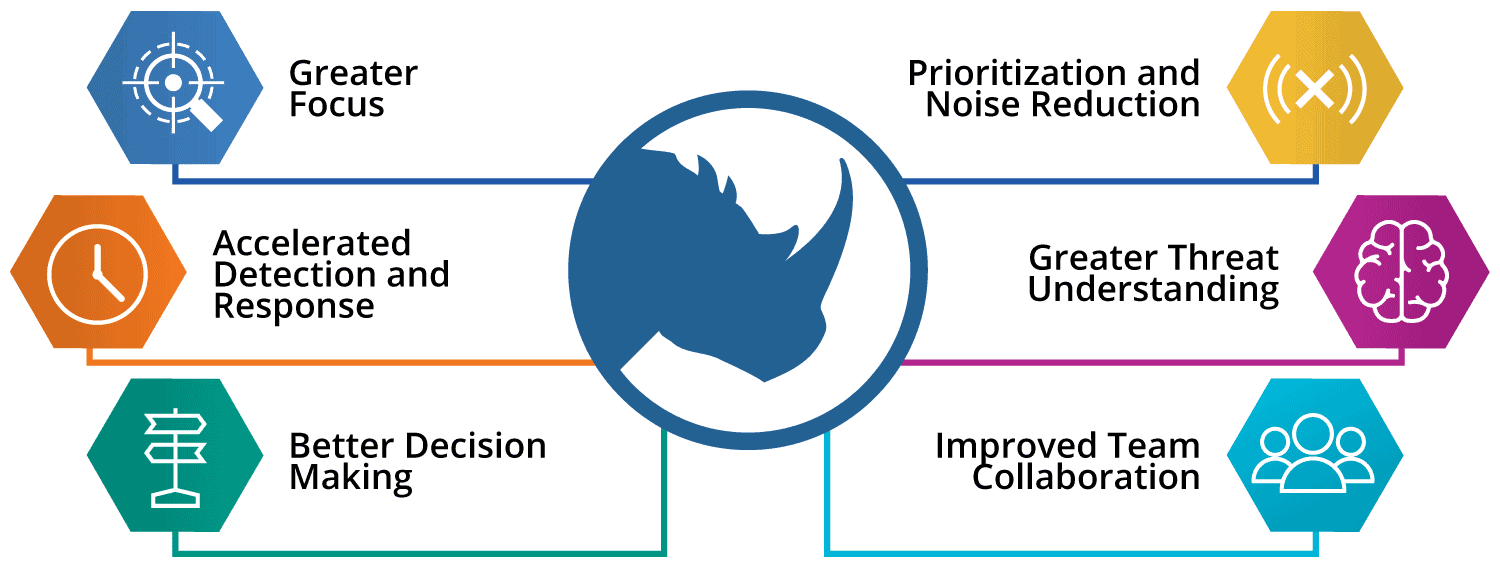
As part of our core capabilities within ThreatQ, we have embedded automation early in the security lifecycle process, aggregating data in the ThreatQ Threat Library and enriching it with context. An automated scoring framework filters out noise and prioritizes intelligence based on parameters you set. With this legwork done, ThreatQ applies only the relevant, high-priority intelligence automatically across your existing security infrastructure – to your SIEM or layers of defense (firewalls, IPS/IDS, routers, web and email security, endpoint detection and response, etc.) or incident response playbooks. This accelerates detection and orchestrates response against the threats that matter most to your organization. To ensure you remain focused on high-priority threats and to reduce false positives, the self-tuning Threat Library automatically learns, recalculates and reevaluates priorities based on a continuous flow of new data and context into ThreatQ.
ThreatQ Investigations provides a shared investigation environment that can include incident handlers, malware researchers, SOC analysts and investigation leads. Incident responders can quickly assess what other research has been performed and by whom, what tasks need to be assigned, and how all the data relates. Through collaboration and documentation, they gain more control over an often chaotic process, and are able to make better decisions and coordinate response to take the right steps at the right time
Optimizing SOAR Workflows
ThreatQ as a SOAR platform optimizes workflows in two ways: ensuring they are informed by contextualized, relevant, high-priority intelligence; and learning as orchestration workflows and playbooks are executed, to continually improve and accelerate incident response.
ThreatQuotient’s key differentiators from other SOAR platforms on the market are:
- Threat Library that aggregates and normalizes external and internal threat intelligence, augmenting it with internal event data and context
- Customer-specific scoring and dynamic prioritization to compare / lookup event and alert context to determine whether it is priority or noise
- Customized Threat Library becomes customer-specific enrichment source ensuring high fidelity and highly relevant intelligence and context
- Captures system and human feedback into central database for instantaneous knowledge sharing
- Learning system that improves and more data and context is learned from both internal and external sources resulting in all downstream processes being more efficient and effective
- Threat Library serves as organizational memory enabling an intelligence capability that can be used across all security operations use cases
- Architecture that allows for deep integrations and bi-directional data sharing, enabling the orchestration, automation and synchronization of cyber threat intelligence across existing technology and teams
- Fosters confidence in data and decisions, which leads to confidence in automation
The Bottom Line
Through automation and optimization, ThreatQ can free-up two to three full-time security analysts for higher level tasks.
This is done through ThreatQ automatically aggregating massive volumes of external threat intelligence from multiple sources (commercial, open source, government, industry, existing security vendors, and frameworks like MITRE ATT&CK) and correlating that data with internal threat and event data (from the SIEM system, log management repository, case management system, security infrastructure, etc.) for context and relevance. Customer-controlled prioritization based on the organization’s risk profile and their own set of scoring parameters brings focus for more informed, faster decisions. With these parameters in place, ThreatQ automatically filters out what is noise for the customer and reveals the right priorities for action.
As new data and context become available and are added to the ThreatQ platform, and teams add observations and documentation from previous SOAR investigations, ThreatQ learns and improves over time. Intelligence is automatically reevaluated and reprioritized so that teams continue to stay focused on what matters in a highly dynamic environment.
